Difference between revisions of "Healthcare Data Security"
BruceHecht (talk | contribs) |
BruceHecht (talk | contribs) |
||
| Line 2: | Line 2: | ||
* 2HDS Healthcare Data Security | * 2HDS Healthcare Data Security | ||
=== Roadmap Overview === | === Roadmap Overview === | ||
The context, working principles, and architecture for healthcare data security is shown in the following diagram. Note the presence of a threat actor potentially compromising security and whose interference the healthcare data security technology is intended to deter, prevent, detect, or mitigate. | The context, working principles, and architecture for healthcare data security is shown in the following diagram. Note the presence of a threat actor potentially compromising security and whose interference the healthcare data security technology is intended to deter, prevent, detect, and/or mitigate. | ||
[[File:Healthcare data security.png|frame|left|Healthcare Data Security Architecture]] | [[File:Healthcare data security.png|frame|left|Healthcare Data Security Architecture]] | ||
Revision as of 10:36, 1 October 2020
Healthcare Data Security Technology Roadmap
- 2HDS Healthcare Data Security
Roadmap Overview
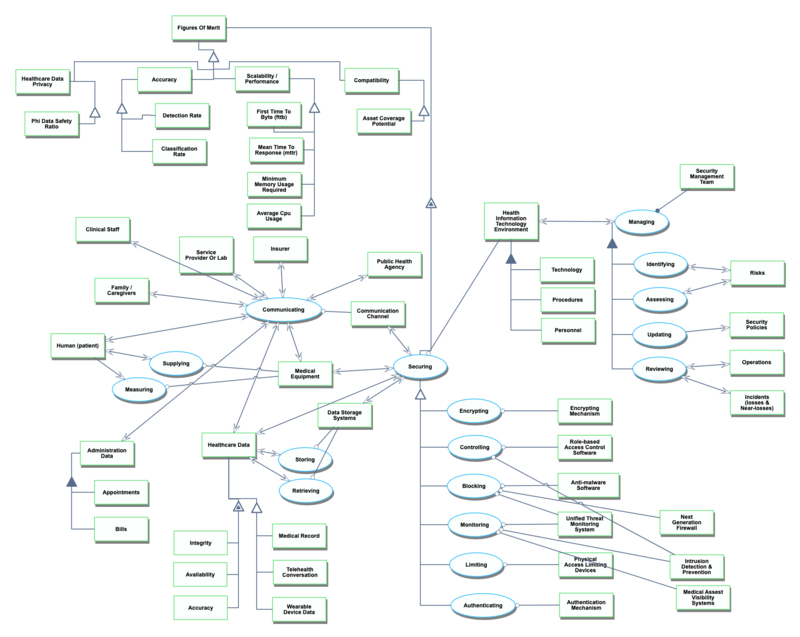
The context, working principles, and architecture for healthcare data security is shown in the following diagram. Note the presence of a threat actor potentially compromising security and whose interference the healthcare data security technology is intended to deter, prevent, detect, and/or mitigate.
Health is an essential aspect of life, connected to each individual and to families and our societies, as well as forming an integrated element of the economy. Distributing healthcare to the point of care may improve outcomes, reduce risks, and reduce costs. Patients, healthcare workers, and healthcare organizations require trust in the security of these systems in order to adopt the systems and to avoid losses. Regulation is primarily made at the national level and requires that health privacy and security are effectively achieved. Compliance to HIPAA requirements apply in the United States<ref name="HIPAA">CDC.gov HIPAA description,“Health Insurance Portability and Accountability Act of 1996 (HIPAA) | CDC.”</ref> , and the EU General Data Protection Regulation (GDPR) applies to operations within EU countries, to data about EU residents, and to any organization that interacts with data of citizens of EU countries.<ref name="GDPR">THE EUROPEAN PARLIAMENT AND THE COUNCIL OF THE EUROPEAN UNION, General Data Protection Regulations (GDPR), 2016.</ref> Healthcare coordination and efficiency may be improved through the use of electronic medical records / electronic health records (EMR / EHR) which may be maintained using on-premises or by using cloud computing services. Over the past decade, increased adoption has focused an attention on the need for systems and technologies to provide for security and privacy while maintaining efficiency and scalability.<ref name="Colicchio_2019">T. K. Colicchio, J. J. Cimino, and G. Del Fiol, “Unintended consequences of nationwide electronic health record adoption: Challenges and opportunities in the post-meaningful use era,” Journal of Medical Internet Research, vol. 21, no. 6. Journal of Medical Internet Research, p. e13313, Jun. 01, 2019, doi: 10.2196/13313.</ref><ref name=Al-Issa_2019>Y. Al-Issa, M. A. Ottom, and A. Tamrawi, “Review Article eHealth Cloud Security Challenges: A Survey”, 2019, doi: 10.1155/2019/7516035.</ref>
This roadmap study focuses on the topic of securing healthcare data, with an emphasis on the virtual world over the physical world, which is largely descoped aside from the stakeholders within the ecosystem for the purposes of this project. The overall objective is to main maintain privacy and safety for patients participating in the healthcare system. Specifically, the technology includes the various tools and methods that allow for the secure transmission, storage and retrieval of healthcare data, with an emphasis on “communication” within a virtual healthcare environment. This includes security controls such as encryption or ransomware prevention capabilities. The roadmap includes security measures aimed to mitigate risk associated with 1) malicious threat actors, purposefully attempting to collect data that these individuals should not have access to, as well as 2) accidental data disclosure, with no malicious intent behind the occurrence. The surface area of assets includes telehealth appoints, wearable devices and medical records.
Design Structure Matrix Allocation
The Healthcare Data Security (2HDS) tree that is extracted from the Design Structure Matrix (DSM) above shows that the Healthcare Data Security (2HDS) is in the context of a larger Healthcare Living System (1HLS) and requires the subsystems of Security Software Systems (3SECSW), Security Physical Systems (3SECPHYS), Physical Data Systems (3PDS). The Security Software Systems (3SECSW) and Security Physical System (3SECPHYS) in turn requires several enabling Layer 4 technologies: Encryption Mechanism (4ENCRM), Role-Based Access Control Software (4RBACSW), Anti-Malware Software (4AMSW), Unified Threat Management System (4UTMS), Least Privileged Access Systems (4LPAS), Authentication Mechanism (4AM). The Physical Data System (3PDS) requires in turn the enabling Layer 4 technologies of: Data Storage System (4DSS) and Communication Channel (4COM).
Roadmap Model Using OPM
An OPM model is provided here for the 2HDS roadmap in the figure below. This diagram captures the main object of the roadmap (Healthcare Data Security), its decomposition into subsystems (Human Actors, Data Storage Systems, Communication Processes that interact with the Communication Channel, Securing Processes that interact with the Health Information Technology Environment, Health Organizations including Insurer, Service Provider or Lab, Public Health Agency, and Family/Caregivers), its characterization by Figures of Merit (FOMs) as well as the main processes (Communicating, Storing, Retrieving, Securing, and Managing). The potential Threat Actor is identified with the potential for the damaging process of Exploiting vulnerabilities in the elements of the system.
An Object-Process-Language (OPL) description of the roadmap scope is auto-generated by the OPCLOUD software and is given below. It reflects the same content as the previous figure, in a formal natural language.